Authentication Boundaries
Demonstrates session-based authentication, protected routes, and access control with an emphasis on how these choices affect server-side trust and exposure.
This project is a focused demonstration of how application-level authentication decisions interact with Linux servers, reverse proxies, and infrastructure security. It is not a commercial product, but a controlled environment used to explore session handling, access boundaries, and secure defaults from an infrastructure perspective.
Demonstrates session-based authentication, protected routes, and access control with an emphasis on how these choices affect server-side trust and exposure.
Uses standard protections (CSRF tokens, password hashing) to illustrate baseline defenses expected by modern infrastructure and reverse-proxy deployments.
Intentionally limited in scope. Advanced concerns (JWTs, OAuth, CAPTCHA, WAF rules) are documented but left out to keep the focus on infrastructure fundamentals.
Screenshots below document authentication flow and system behavior. Visual design is intentionally minimal to keep focus on access control and infrastructure impact.
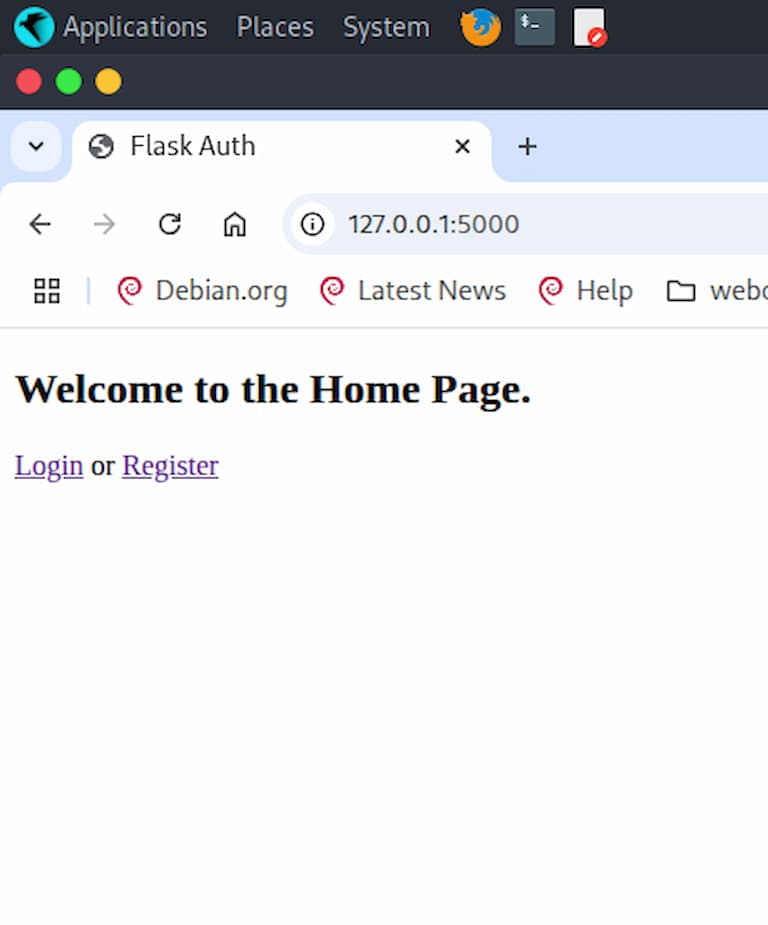
Homepage linking to registration and login flows.
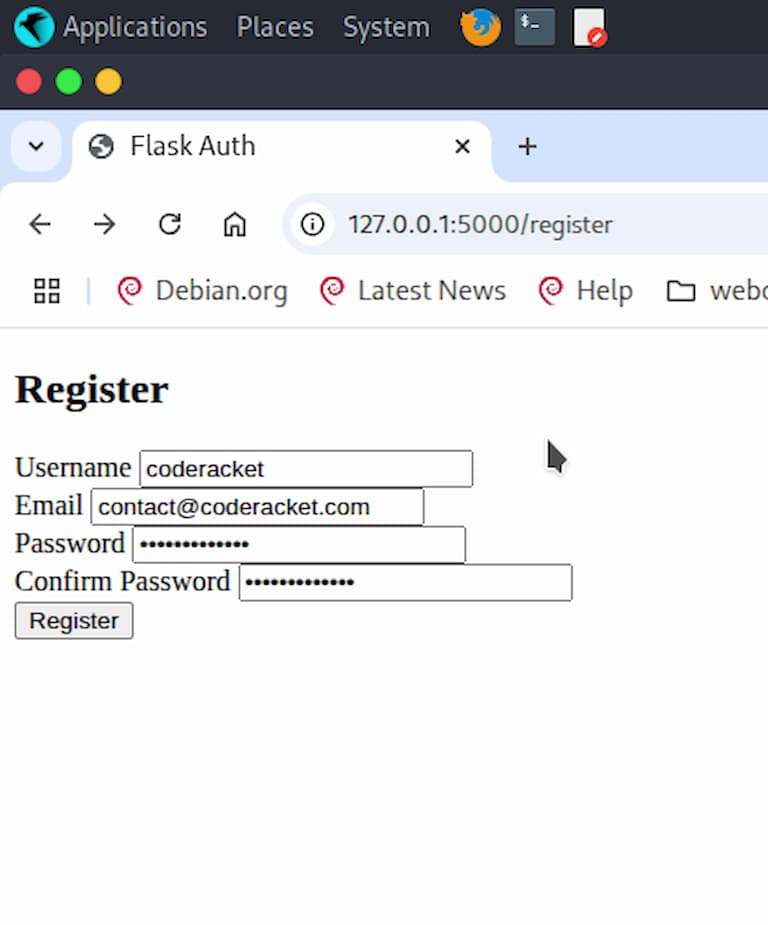
Registration with server-side uniqueness enforcement.
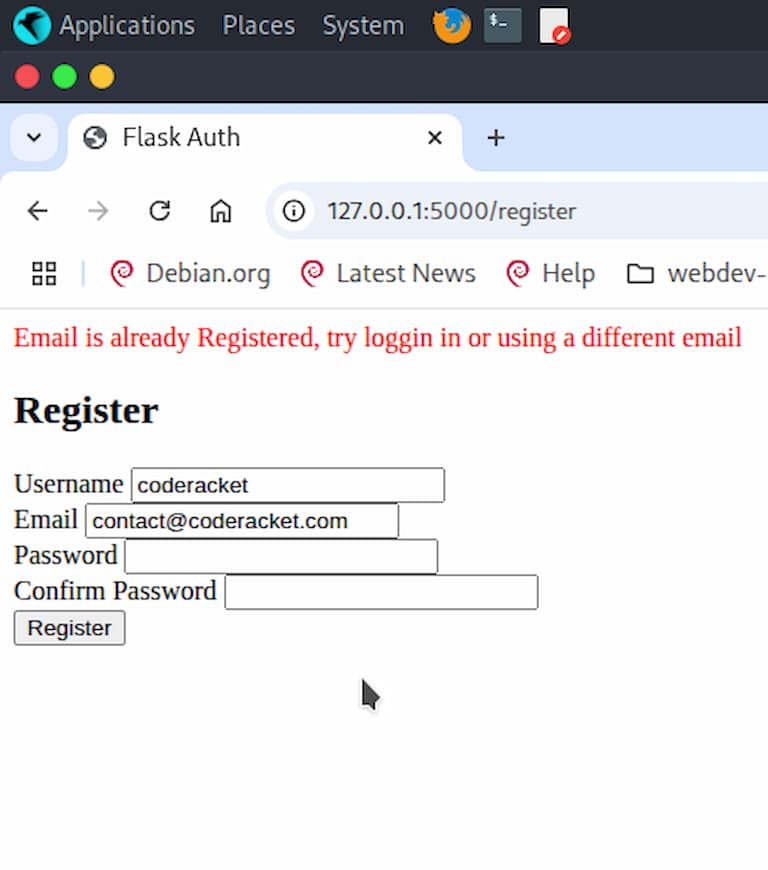
Explicit error messaging shown intentionally to discuss information disclosure tradeoffs.
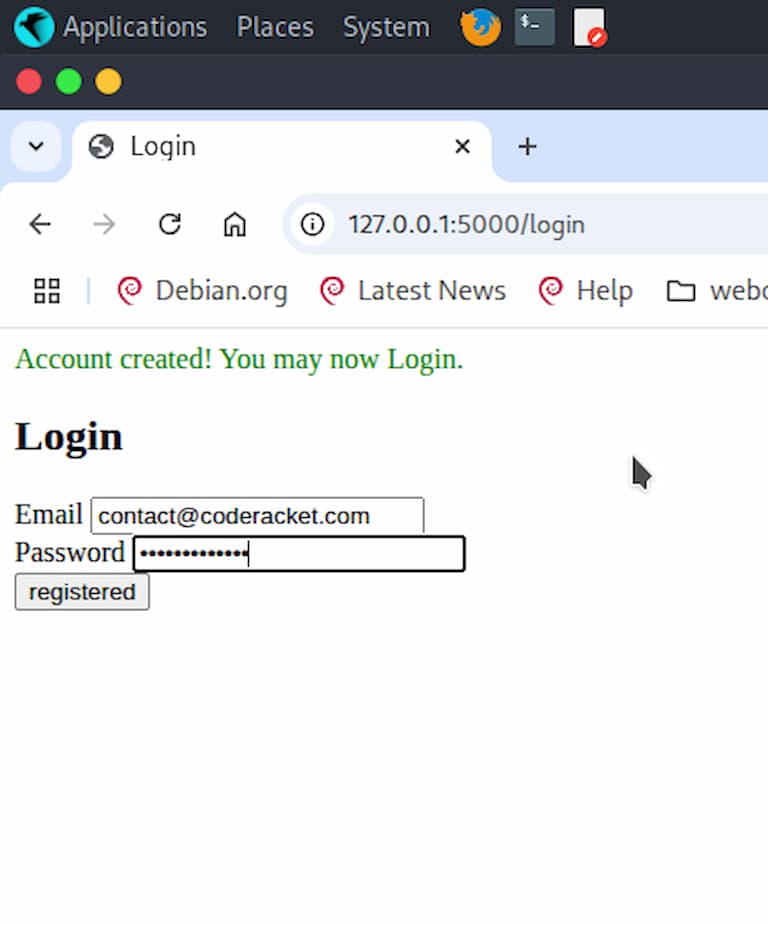
Login flow enforcing session-based access control.
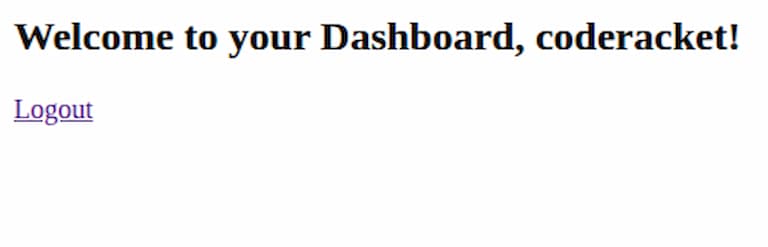
Minimal dashboard — UI intentionally deprioritized in favor of auth flow clarity.
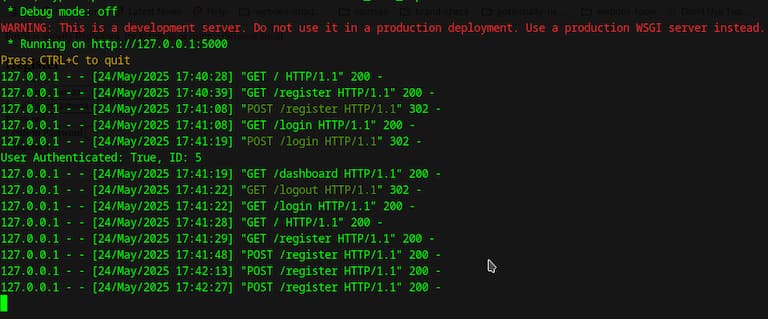
Local containerized runtime — used to mirror infrastructure boundaries.
Interested in working together? Reach out via email or LinkedIn.
Email Me LinkedIn